Social engineering is designed to evade common security setups by targeting the people inside organizations — relying on human error as the weak link. While hackers’ approaches behind social engineering may differ in form, their goals are all very similar: identity theft, data breaches, ransomware attacks and more.
Phishing, one of the most popular forms of social engineering, is becoming more common with each day. It is very important to educate ourselves about cyber security to ensure our individual and institutional data remains protected. Equipping ourselves and the University of Toronto (U of T) with sophisticated and advanced tools is only half the battle. We can be proactive in preventing data breaches and other attacks by staying educated and aware, and therefore avoiding potential for human error.
Recently, there has been an influx of phishing emails containing malicious links targeted at U of T community members. These attacks have been impersonating U of T administrator roles and targeting unsuspecting community members.
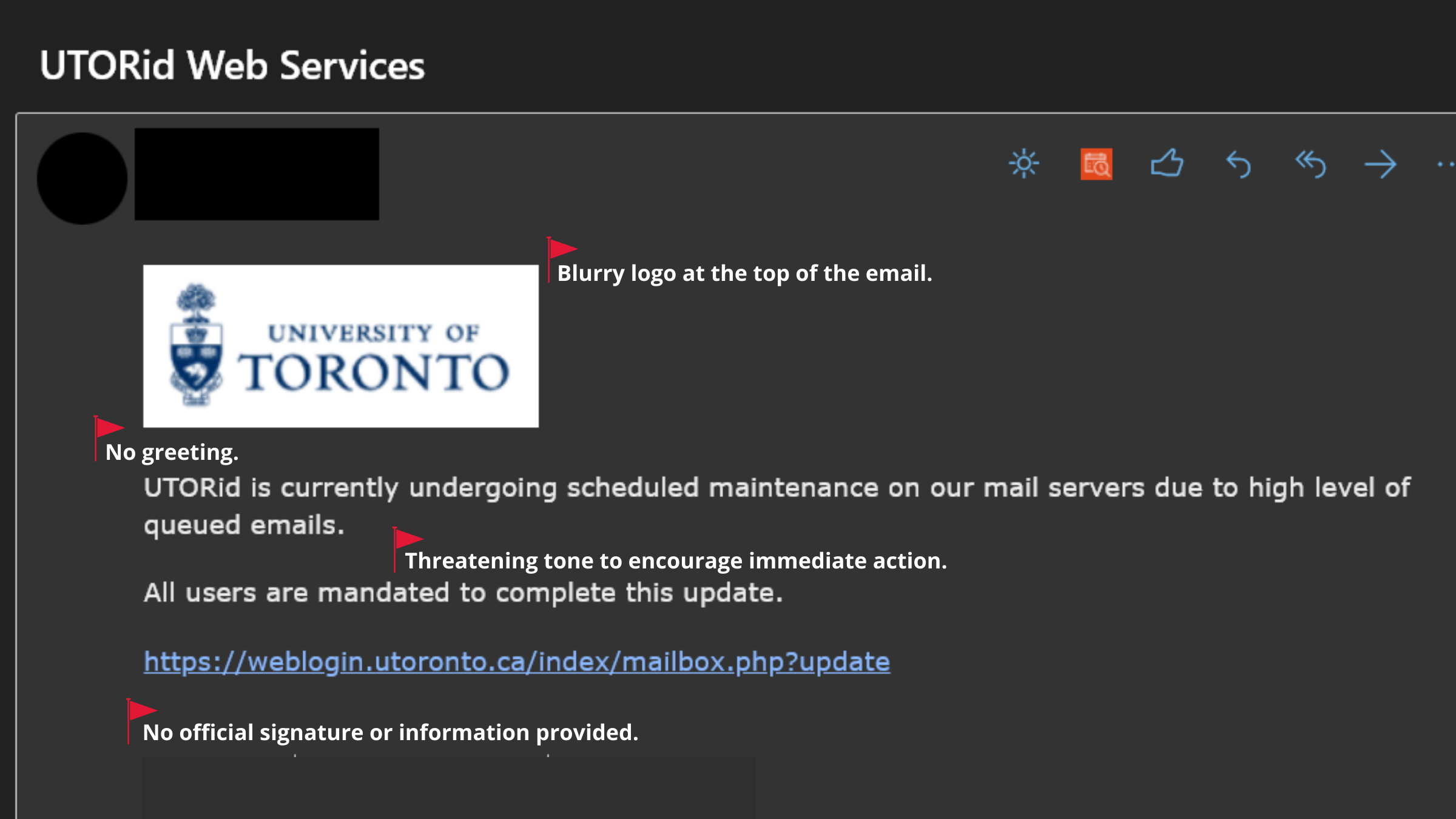
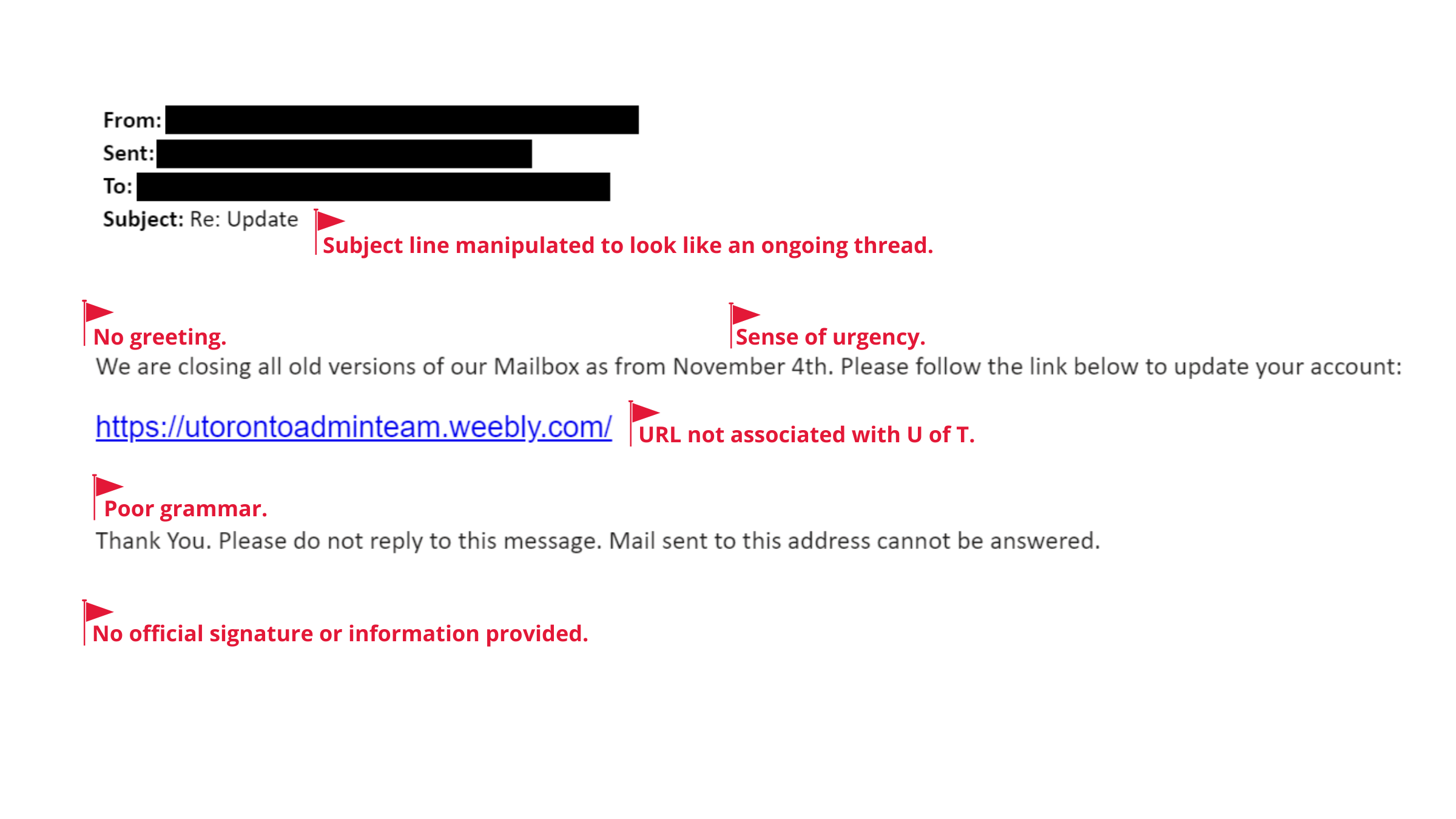
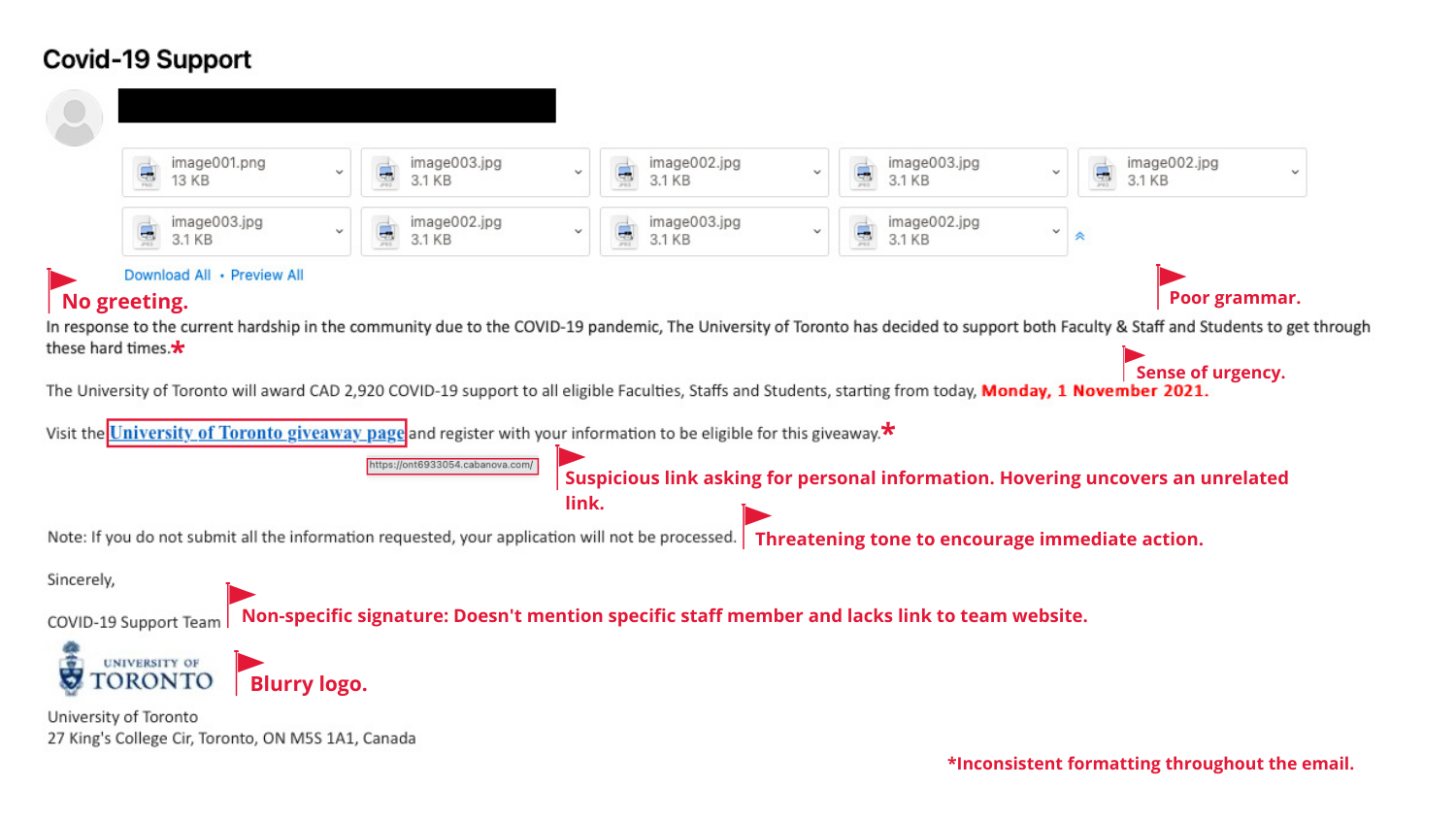
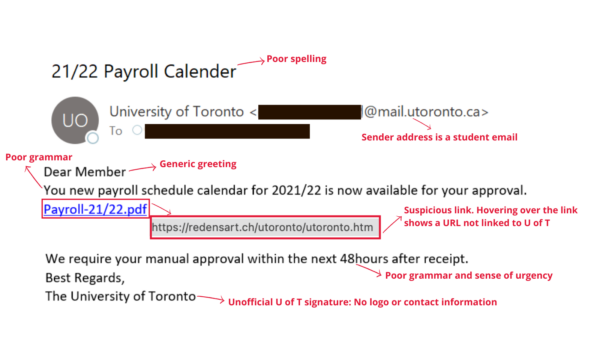
Below are two recent emails that were sent to U of T community members. Review the red flags to help you understand the anatomy of a phishing email:
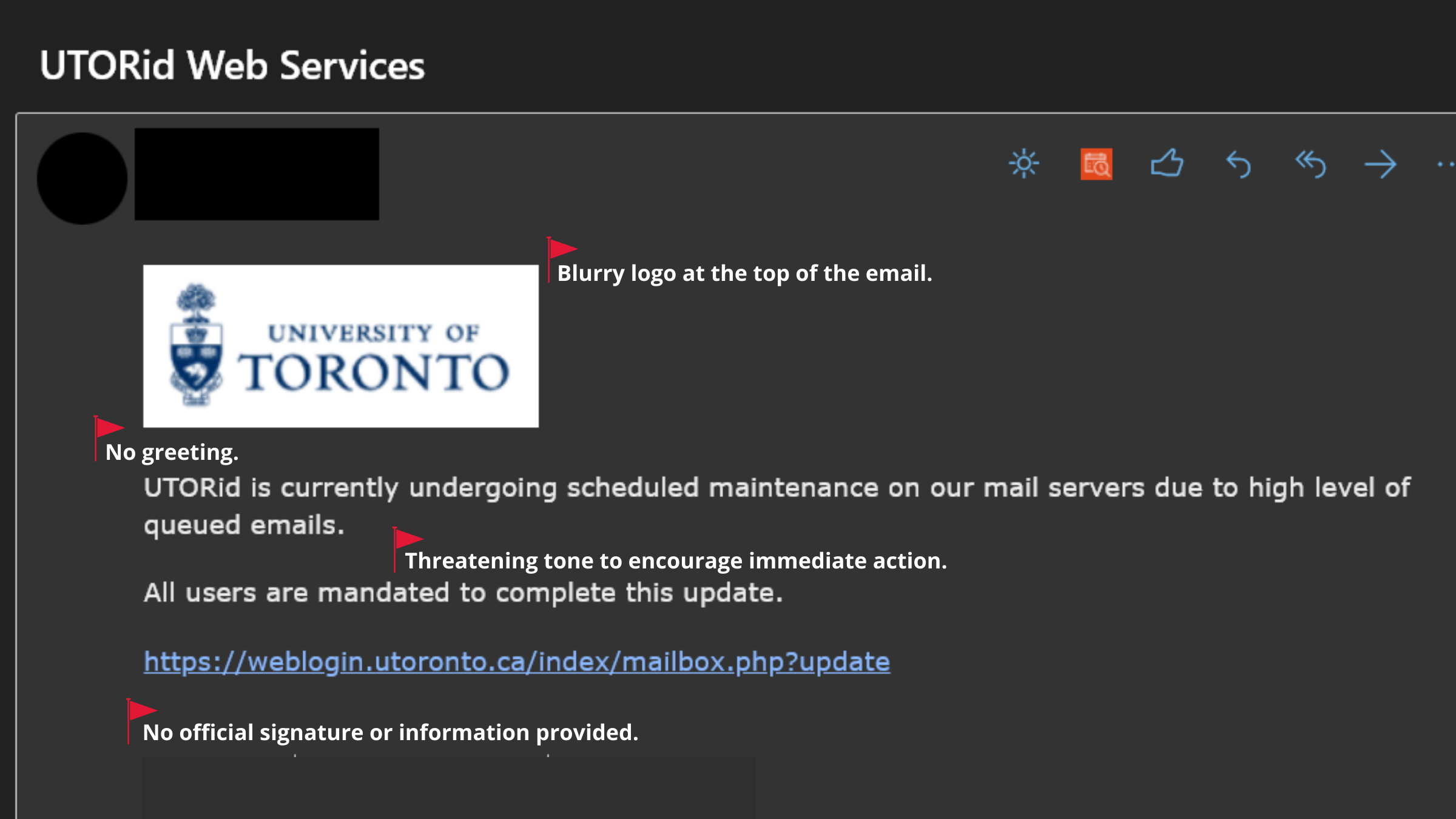
Image 1: This recent phishing email contains a malicious link to a spoofed UTORid web page. The email was sent from an email address impersonating a U of T staff member.
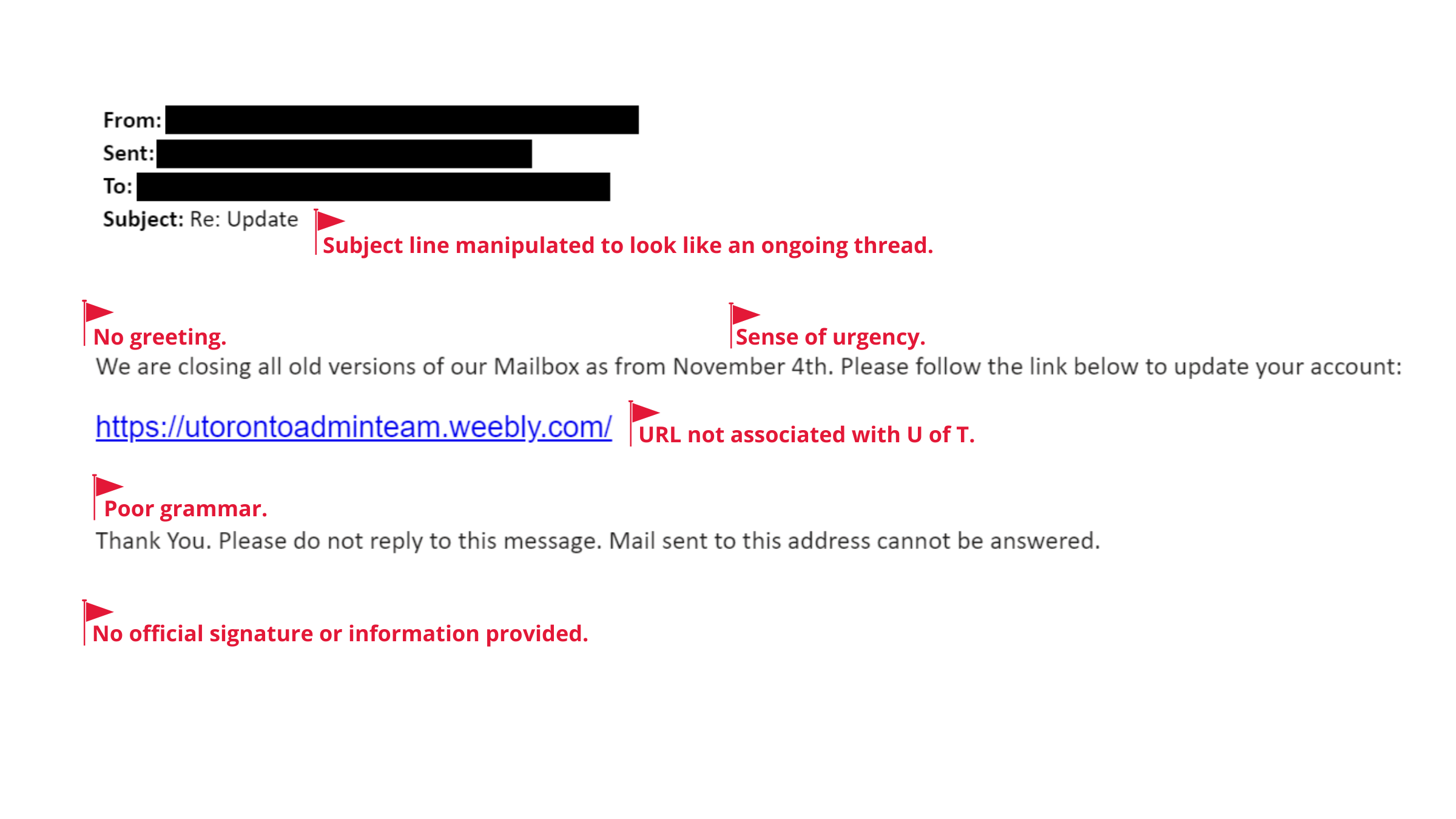
Image 2: This email prompts U of T community members to click on a link to ‘update their account’.
At first glance, phishing emails often look like legitimate communications from a trusted organization. No matter how real it looks, treat every email you receive with caution — especially ones you weren’t expecting to receive. In the case of receiving a suspicious email, review the common red flags to identify if action is required to report and remove the email.
If you receive a suspicious email, ensure you report and delete the email immediately.
For information on how to report a phish, visit https://securitymatters.utoronto.ca/report/.
Visit the Phish Bowl and the Security Matters blog to read about recent phishing attacks within the U of T community.