As remote work and online classes are increasingly becoming a gateway for advanced cybercrimes, it is important that members of the University of Toronto (U of T) community stay aware of how to spot and report phishing attacks.
This week, members of the U of T community including employees, faculty and students received a voicemail-to-email phishing attack, which was successfully thwarted. The email contained an attachment with a malicious link and was marked as ‘External’ to mislead the recipient into thinking it was sent by a trusted external source.
The image below marks the red flags to look out for:
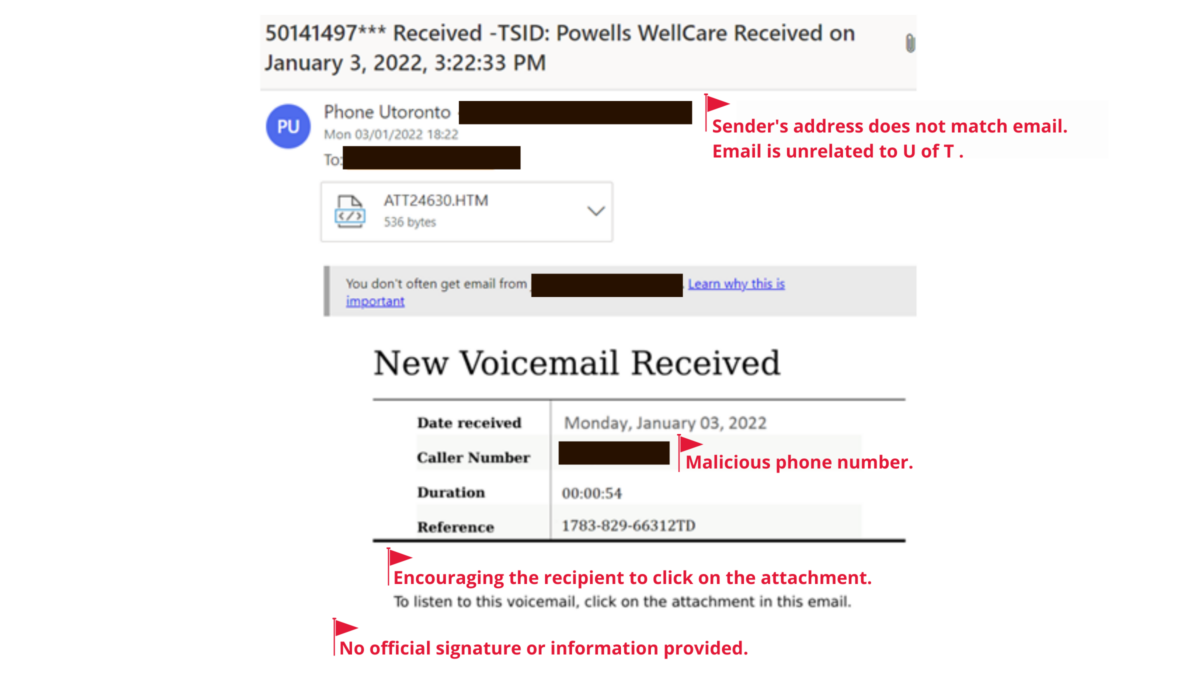
Image: The email asks the recipient to click on the attachment to listen to the voicemail, which is a malicious link to a .HTM file.
If you receive an email like this or other suspicious emails, please do not click on any links or download any files from the email. Make sure to report suspicious emails to report.phishing@utoronto.ca and brush up on the common red flags so, you know what to look for.
To learn more about the recent phishing attacks and how to keep yourself safe online, visit: https://securitymatters.utoronto.ca/.