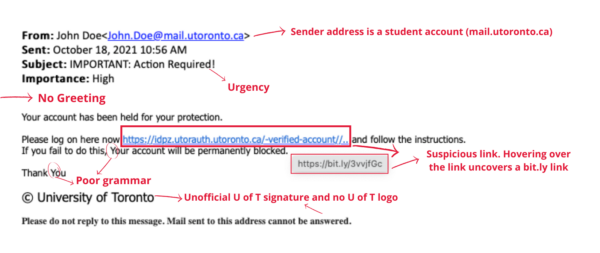
Phishing continues to play a big role in the digital threat landscape. To further enhance the University of Toronto’s (U of T) cyber defences, we are highlighting a recent cyber attack that was successfully thwarted on Oct. 18. U of T community members received a phishing email where the hacker impersonated a U of T administrator role. Suspiciously, the email came from a fake U of T student email, ending in mail.utoronto.ca. The attack aimed at retrieving the user’s credentials through a link, which at first glance looks legitimate, but was obscured using a URL shortening feature.
Although, the attempt could seem sophisticated, the hacker used a few telltale signs of a malicious email:
- Email spoofing: This is a technique used in phishing attacks to trick users into thinking a message came from a known and trusted source. In these attacks, the sender forges email headers so that the email displays the fraudulent sender address. In this instance, the sender was pretending to be a U of T administrator, however the email address used was a student email.
- Sense of urgency: Evoking a sense of panic, urgency, or curiosity is a commonly used tactic to scare recipients into giving up confidential information. The email subject and body suggest urgent action requirement and the recipient’s account being locked if they don’t click on the link.
- Requesting personal information: The copy asks the recipient to log in using the given link, which is another telltale sign used by hackers to steal credentials, leading to further damage such as identity theft, loss of other information and more.
- Suspicious links: The URL in the copy contains terms such as ‘utoronto’ and ‘verified-account’ to make it seem legitimate, however a suspicious bit.ly link is exposed when hovering over the written link. Hackers use URL shorteners, such as bit.ly, to bypass email filters and trick users to click on malicious links.
Phishing attacks can take many forms, but they all share a common goal – getting you to share sensitive information such as login credentials, credit card information or bank account details.
Here are some steps you can follow to in the case you receive a suspicious email:
- Report phishing messages by either using the “report message” function in your Office 365/UTMail+ inbox or report it to report.phishing@utoronto.ca.
- When in doubt, call or ask the sender in person to confirm that the email was really from them.
- If you opened an attachment that was provided in a phishing email, contact to your local IT service desk immediately.
- If you suspect your password may have been compromised due to an attack, ensure you immediately change it.
Visit here for more information on identifying and reporting a phishing attempt.
