Phishing attempts and attacks are incredibly common forms of social engineering, used to target people in the form of malicious emails or messages. These attempts are becoming more sophisticated and polished and are on the rise as more people work remotely. Here are steps to identify and report phishing attacks.
What can I do if I suspect a phishing attempt?
- Report phishing messages by either using the “report message” function in your Office 365/UTMail+ inbox or report it to report.phishing@utoronto.ca.
- When in doubt, call or ask the sender in person to confirm that the email was really from them.
- If you already clicked on the link or attachment, contact security.response@utoronto.ca and your local IT service desk immediately for assistance.
- If you suspect your password may have been compromised due to an attack, immediately change it.
What are common red flags of phishing attempts?
A strong sense of urgency and/or odd requests
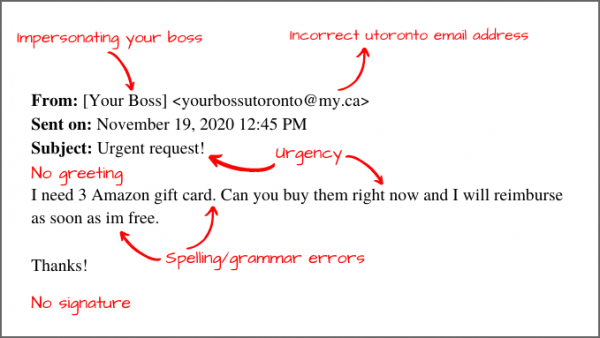
These emails will often request that you complete a task quickly so that you don’t have time to consider or think about the request. A common example is when attackers pose as the victim’s boss and ask them to quickly purchase a gift card and send the code via email. See an example here.
Requesting personal information
Legitimate organizations are unlikely to request sensitive or personal information through email, so a request for this information is often a sign of a phishing attempt. University of Toronto (U of T) staff, faculty and students will never be asked to share their UTORid password.
Spelling and/or grammar mistakes
Check for spelling mistakes and/or grammatically incorrect sentences. If you are already suspicious, these mistakes can be an indication of a phishing email. See an example here.
Brief signatures and generic greetings
The email signature may be missing crucial information like an address or phone number, while the greeting may use phrasing such as “good afternoon,” “dear customer” or no greeting at all rather than your name. See an example here.
Intriguing attachments or links
Phishing emails aim to trick you into clicking malicious links or opening malicious attachments. The attachments might even include fake images or icons to make it look like the sender is sharing or sending a document you are expecting. Fake links might be hyperlinked so that the display text seems legitimate, but the hyperlinked address is malicious. See an example here.
What can I do to help identify/confirm a phishing attempt:
- Tap or click the display name to see if the email address matches/is valid
- Hover over (or long-press on mobile) links to check if the URL address matches the display text
- Check the Phish Bowl to see if the email you received has already been reported
What can I do to prevent future phishing attempts?
- Enrol in UTORMFA, U of T’s multi-factor authentication solution to add an extra layer of security yo your login. Learn more and self-enrol in UTORMFA.
- Pay attention to the email notification banners that helps staff, faculty and students identify emails originating outside the University.
- Connect to the appropriate Virtual Private Networks (VPN) to help secure your access to sensitive systems and protect yourself when connecting from remote locations.
