Phishing emails are designed to trick recipients into taking an action, such as clicking a malicious link or opening a malicious attachment. Hackers may also use tactics like smishing, which attempt to trick the recipients through text messages or SMS.
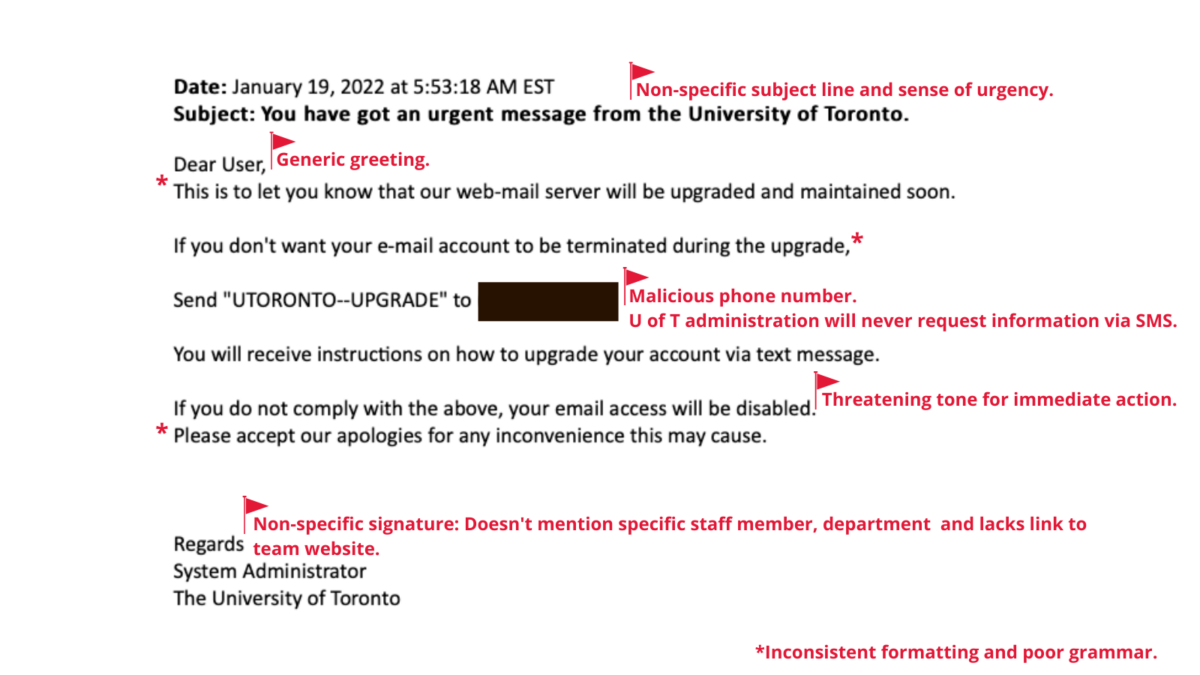
This week, members of the University of Toronto (U of T) community received an email impersonating U of T’s IT administration that asked recipients to respond through SMS. Please note that any technology upgrades or updates will always be communicated by your division or department through official U of T channels prior to deployment.
Sense of urgency is a big factor that hackers use to get recipients to take action. You will be able to identify and report phishing by taking a moment to review your emails for common red flags.
The image below marks the red flags to look out for:
Hackers are constantly adopting new techniques to steal information, so it is imperative that we stay alert and aware to better protect ourselves online.
What to do if you receive a suspicious email
- Review the common red flags.
- Do not act on any of the email prompts including clicking the link, providing personal information, opening the attachment or sending SMS.
- Forward the email to report.phishing@utoronto.ca and then delete it from your inbox.
- If you already engaged with the email, please contact security.response@utoronto.ca immediately for assistance.
Visit the Security Matters website for more information.