This week, a department at the University of Toronto (U of T) received an especially sneaky phishing email. The email used many of the hallmarks of social engineering in an attempt to manipulate recipients into clicking on a malicious link that appeared to be from the department’s manager.
Luckily, members of the department recognized that something wasn’t right, and reported the email to Information Security staff. Can you spot the signs and characteristics of a phishing email? We spotted at least seven.
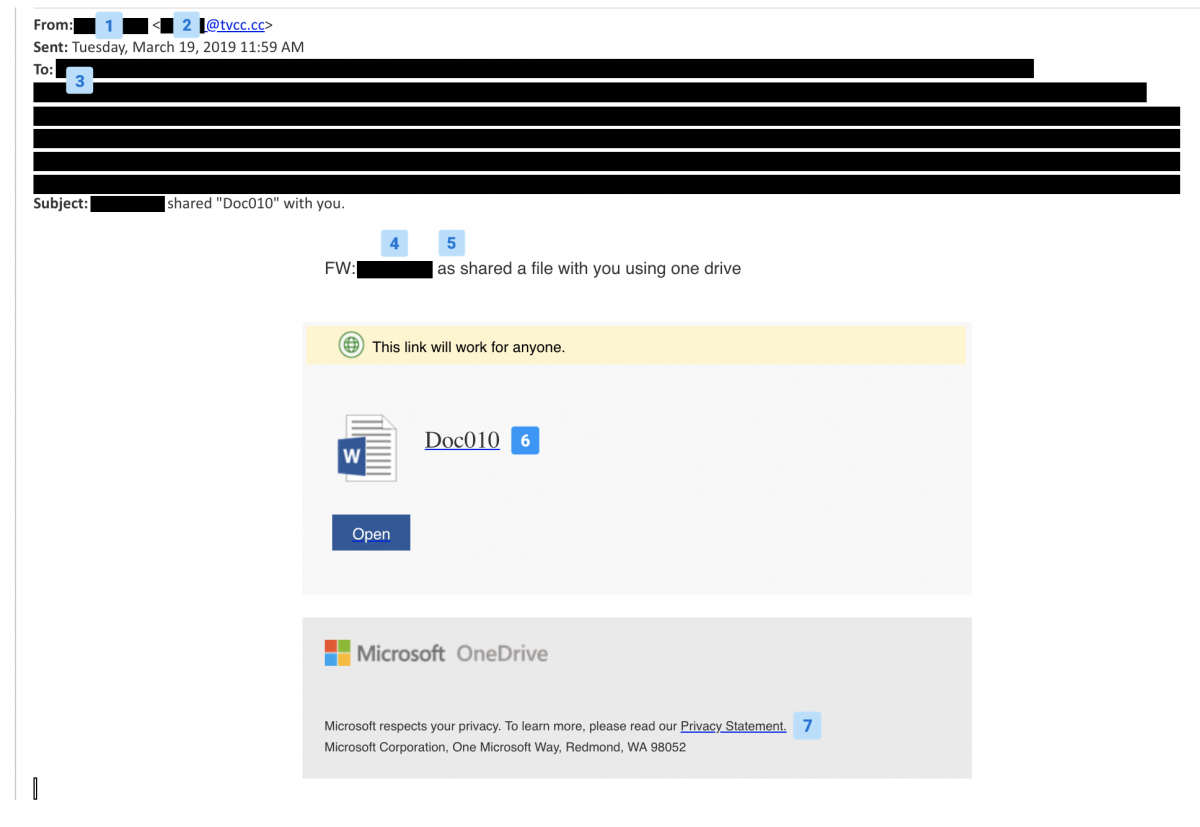
- The email was sent from someone who shares the first name of a department member. While this detail is small, in uses social engineering techniques to generate a sense of familiarity for the recipients
- The sender’s domain does not belong to U of T. Never open emails from suspicious domains. Even if you do recognize the domain, it doesn’t mean the email is safe: hackers regularly spoof email addresses to make it seem like they are coming from legitimate sources.
- The individuals that received the email are all current members of the same department, but it didn’t make sense for everyone to receive this email from an unrecognized source. Using related and legitimate institutional email addresses is another common social engineering exploit: the recipient list only contained legitimate and related U of T email addresses.
- The body of the email uses the department manager’s name and says that they have shared a file with the recipient list. This is another trick intended to make the email seem more legitimate.
- There is a typo in a strange place. Typos are synonymous with phishing emails.
- The document link is to OneDrive, but it is not U of T’s Sharepoint. If you hover over the email link you can see that the document link leads to a non-University Sharepoint domain.
- The email adds a Microsoft OneDrive footer with a privacy statement link to add legitimacy to the email, but the link is suspicious. If you hover your mouse over the text you will see that it leads to a strange URL.
To report a suspicious email or phishing attack, contact report.phishing@utoronto.ca.
For more tips on how to stay safe online at work visit our Security Matters blog and check out our tip sheets.